The Assurance team convened at Munich on the event of the ATE, also coinciding with Audit's final event in evidence gathering.
Next meeting: Assurance MiniTOP - Hamburg 20091215
Present:
Meeting started 12:00, finished 18:00. Location: Ted's patio. Refreshments provided by Ted + Renata.
Minutes & agenda taken by Iang. Reviewed at end of meeting. (Agenda was also previewed informally in meeting previous night at hotel.)
Costs:
Type Amount Comments Hotels 338.70 5 nights (Iang x 2, Dirk, Sebastian, Ulrich) Dinner 51.00 5 meals (Iang, Dirk, Sebastian, Ulrich, Werner) Train 63.50 Sebastian Total 432.20 Also included ATE
Probable additional component of costs for this meeting is closer to 280 euros as Audit was covering the ATE. Also included: ATE, auditor assurances, as final leg of Spring tour.
Presentation of the results of the 'Spring Tour' of Europe by Iang for the purpose of gathering evidence over the Assurers.
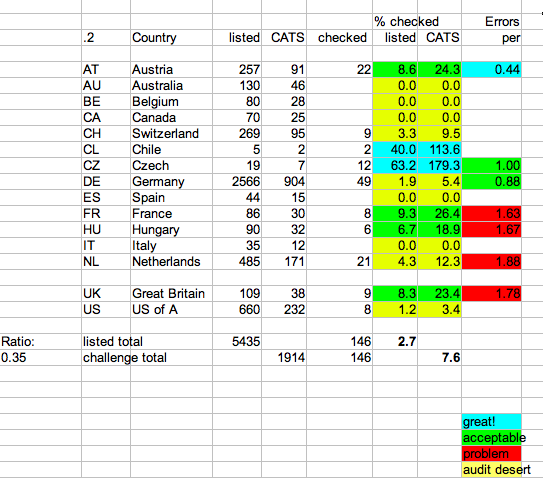
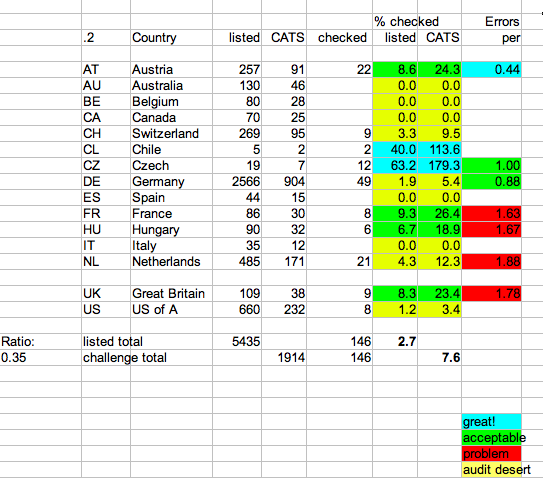
Above image is snapshot of the spreadsheet used to collect evidence results.
Statistic Measure Locations visited by Auditor 13 (9 recently) Locations reviewed by Assurers 4 ??? Total Locations 17 Countries reviewed by Auditor 8 Assurances audited 146 Coverage 7.6% against CATS Estimated Cost €2,000 13 per
The following implications are clear:
A.2.y The CP details how the CA verifies that RAs operate in accord with the CA's policies.
Assurance needs to be much stronger. Therefore, the conclusion is that Assurance needs to audit itself:
Assurance needs to be Self-verifying.
Given that goal, the following methods are advised:
End of Audit's report on evidence-gathering phase. Now meeting moved onto the list of items on agenda and generated above.
As per the report, we have developed this procedure to audit the assurance. Ulrich prepared and used a template in Bielefeld using colours, questions, names. We should write up the process for auditing the Assurer. Should be based on the experiences of ATE/Audit Spring Tour. Ulrich has already taken the process used at CeBIT and formalisted it. Iang did the same thing a different way. Combine them. We need a practices document or somesuch.
Ulrich & Iang to write. Here.
Terms for Officers aren't good. The term "officer" implies power where none is really granted. It results in title-seeking.
Other terms: speaker. Team leader is popular These are terms that reflect the work better. Propose that Events coordinator can be Events team leader. No easy term for Assurance Officer discovered.
Ulrich to propose.
Ted asks for fresh eyes on the handbook. Ulrich says maybe this summer, after ATEs. Ask at each event, Ulrich to ask at the ATEs.
The old document that described this was reviewed.
What is the appropriate bar for this? Round table:
All are in principle agreed to move forward on it.
Sebastian as Assurance Officer to propose. Posted.
It should be possible to re-do the assurances. Assurance points can currently only be awarded once.
Points that are aged can be topped up by the re-assurance.
System should be patched so that instead of showing "you can't do that" it shows the information for the assurance so that the Assurer can work with the situation.
Audit and other purposes needs a way to get a reliable statement from the Assurer over some issues, such as the criteria or the ATE reports. We need a symbol to show this, like "Fred, CARS" where CARS stands for CAcert Assurer Reliable Statement. Suggested it should be fishy, like COD. Perhaps CARP, CAcert Assurer Reliable Proposition.
Sebastian. Plus iang.
Long discussion over CAP forms. Decision to fix the old one, if possible. Sebastian is arbitrator on the case filed against the CAP forms.
asked Dirk to look at the code, Ulrich to fix.
The words "I agree to the CAcert Community Agreement" should be on the form. Probably above the Member's signature block.
If possible, thanks Dirk!
Also, "This assurance has been completed according to Assurance policy". Both these onto the OLD form.
Translingo problem, can we expedite the translation of the term "I agree to the CAcert Community Agreement" text?
Ted, Dirk, Ulrich encouraged to join the association. Ted & Ulrich filled in the forms and paid Iang €7.50 each for onwards payment to Robert Cruickshanks (has an Oz account) as $10 US each. Forms signed by Sebastian, need to find a seconder. Dirk indicates in some months.
Iang to forward forms to PD and payments to Robert/CAcert Inc account.
Arbitrators. We need more. Ted is busy. Sebastian has asked someone but not yet, person busy. Should an Arbitrator be a Senior Assurer? Probably. Arbitration is good, it is working, but it is too slow. Need faster tools for simple actions.
Note for PD: Pete Arb? Check all arbs.
Arbitration needs better support, need more support engineers, if you want better support, Arbitration should expedite the support engineer background checks :)
How professional is the support system working? 1st level is team of SEs who get in the issues and work it JIT. Other problems that can't be done at level 1, and should be moved to level 2. E.g., system related access is needed. Technical issue but nobody knows about. Only one guy working the 1st level means that it is hard to split the team into two levels. Need to construct a team who can work the mailing lists / ticket system.. to first interact with the issues. Put more traffic to the support list: Fast turnaround but open. Less traffic for the support email: Slow but private.
Ask for more SEs? Instead of Arbitrators. Need people who have the technical knowledge, certs, CAcert etc. Need to ask the people to join the open support list. They need to understand the responsibility of the position and how it supports CAcert.
Review this issue in a month or so, chase new people for the team. If the support issues are not a big problem, revert them to the open mailing list.
The Assurer can request the reset of password. This has been requested before in the past says Assurance team, it is a normal problem that the Assurers have wanted solved because lots of people who come to events have this problem. The assurance is lost when the person's account is blocked.
Agreement in principle with concept:
An Assurer can request a password reset of a Member if the Assurer has done an asssurance over the person (or equivalent if already assured).
Dirk: Add a patch to the "you cannot assure a person twice ..." so that the information of the prior assurance is displayed. Ted needs to see the points of the Assurer in order to check that they are full Assurer for the CATS certificates.
Status of Member should be available to Any Assurer. Any Assurer can already see a rough status of any Member (not exact) because they can pretend to do the Assurance. Should be able to see: 0, 1, 50, 100 Assurance points, Assurer, 50 Experience Points. In Privacy Policy, the Member's status is published data so no privacy problem. Any Assurer, only.
The BirdShack team should have these requirements.
Try to route some traffic from support@cacert.org to the mailing list. Something like "It is faster, but don't send any delicate data."
Under the age of 18 as Assurer. The question is whether the Assuree enters the CCA which is not easy for the underage / minor. Therefore for the minor, there must be a co-signatory on the first CAP form to accept the responsibility.
What ages? The consensus for Member was: 10 years. Rationale was younger children don't have the ID docs. This is the age where children enter high school so there is a shift in responsibility and IT exposure.
The consensus for Assurer was from age 14. Rationale: Germany: accepts contracts for minor things, it is legal to work. 14 is half way from 10 and 18. In the Church tradition, 14 is the normal age of confirmation. Can only issue maximum of 10 Assurance Points.
At age of 18, there is no limit based on age.
Co-signatory: for Junior Assurer: can be a parent/guardian or any adult CAcert Assurer. The Assurer must notify the parent/guardian of the situation. The details of how to do this securely are left up to the Assurer, as he is responsible.
(Post meeting note: Hmmm, this does not apply for Junior Member. What is the story there?)
Tverify is discussed. There is no subpolicy, AP doesn't allow it so it will be stopped when Audit hits it. Tverify subpolicy is a wip with Guillaume. A start was done in Paris 20090503. Ask him how it is going.
Remote/TTP. Summary... What to do about Remote/TTP ? Do we care? Germany doesn't care. Will ease the task of seeding Assurers.
Super-assurances are to be identified and deleted. Assurance Policy allows more EPs to be assigned temporarily. So there is still a possibility.
The "special" Assurance Points from Super or TTP etc should age, probably more quickly than ordinary points. Or disappear entirely. Maybe age to zero over one year? Look at a script to wipe out the effect of Supers, either set them to 35 or delete them.
Dirk???
Problem with the TTP table, already complex. General skepticism about the current efforts to make this happen, it looks like the subpolicies cannot resolve the difficulties. So, concentrate the energies on other things?
We have a big problem in communicating with the Assurers. Is it hard? No, just look at the script that does the statistics. Might be easy .. ok, do it. It is no longer an audit issue because the system blocks these non-Assurers already, that's a control.
This is a much bigger issue, it is a blocking issue for audit . Without it, CAcert has uncertain contract arrangement, has not even taken the customary step of notification. If notification is done, then at least this is the minimum. There is less need for confirmation of the acceptance, also there is less need to handle the response. The main thing is that Members know.
Decision: write a patch to notify all Members of CCA. Provide a patch to ease up the account deletion issue.
Dirk to do it.
The other thing wanted by audit is to add a checkbox "[] I agree to the CAcert Community Agreement" to the certificates request processes. The strategy here is to add the checkbox to all places where CAcert important services are demanded, rather than on entering the account. This is also matched by the CCA which lists 5 places where agreement is made.
Dirk, are you still with us?
Ulrich has access to the Edu directory only. Asked Henrik, said no. Events directory is under PR. This has to change, the reports are needed, not bureaucracy.
Ulrich to write to PG directly, also add Sebastian. Apparent lack of helpful responses. Set up a separate Events directory.
Is there scope for a set of principles in Assurance?
Ted says that the PolicyOnNames was an attempt at that, but things have overtaken that. Rename the PolicyOnNames to PracticesOnNames, and relink it.
Ted to rename it, look at the principles.
Meeting ended 18:00.